overview: the best, best, cheapest options
when building a malaysian server for companies to use for charging and accounting docking, they must not only pursue the best stability and compliance, but also hope to find the cheapest but safe solution. the best solution is usually to choose a hosting service with local compliance qualifications and financial audit support, which can not only ensure the traceability of transaction links, but also reduce cross-border tax and regulatory risks; the cheapest solution can consider cloud hosting or vps, but additional compliance and security controls must be invested to avoid legal and credit costs due to cost savings.
compliance and legal requirements
when enterprises deploy malaysian servers in malaysia for recharge and account docking , they must first comply with local financial supervision, telecommunications and data protection laws (such as the personal data protection act pdpa). the compliance process should include customer identification (kyc), transaction limit management, suspicious transaction reporting, and time limits for retaining accounts and logs to ensure that a complete chain of evidence can be produced during audits.
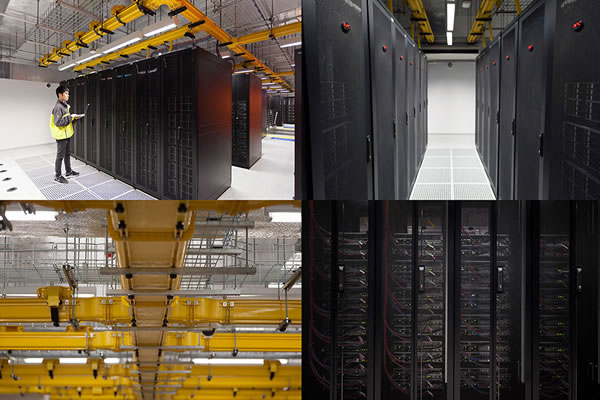
server selection and deployment recommendations
choose a malaysian server type based on the size of your business: cloud vps is an option for small recharge businesses to save costs; independent physical or managed servers are recommended for medium to large or high-frequency trading businesses to improve stability and controllability. pay attention to network bandwidth, redundant links, data center compliance certification (such as iso/iec 27001), and whether the provider supports api and port security policies required for cross-border account docking.
security and access control
security is the core: implement the principle of least privilege on the server, enforce multi-factor authentication, network isolation and firewall policies, and implement rate limits and ip whitelisting for key interfaces. enable tls encryption for the deposit and settlement interfaces. the database uses column-level encryption to store sensitive financial data. the logs must not be tampered with and backed up offsite to facilitate subsequent audits and evidence collection.
account docking architecture design
account docking should use standardized apis and message queues, and clarify transaction serial numbers, status callbacks, and retry mechanisms. the design should distinguish between the transaction processing layer and the accounting layer: first record the original transaction data in the temporary table, and then enter the formal accounting system for accounting, reconciliation and cashier operations after confirmation by the third-party payment or operator to ensure consistency and traceability.
reconciliation and audit process
establish a day-end and month-end reconciliation mechanism to automatically compare server transaction logs, third-party payment settlement documents and local accounting vouchers. reconciliation differences need to form a problem ticket and be handled by a dedicated person, and all processing records will be included in the audit trail. regularly hire a third party to conduct security and compliance assessments to ensure that processes and systems are updated to meet compliance requirements.
sop and division of responsibilities
write the compliance process into the standard operating procedures (sop) to clarify the responsibilities and authorities of front-end recharge, risk control review, financial accounting and exception handling. set up authority isolation to prevent the same person from having the authority to initiate transactions, review and financial confirmation at the same time to reduce the risk of internal fraud.
backup and disaster recovery strategy
implement cross-availability zone backup and off-site disaster recovery, and regularly practice the accounting recovery process to ensure rapid switching and ensure the integrity of accounting data when the main server fails or is banned. the backup strategy needs to take into account the recovery point objective (rpo) and recovery time objective (rto), and include backup credentials in the compliance retention list.
third party and contract management
sign clear contracts with cloud vendors, payment channels and local agents to agree on service levels, data processing responsibilities, audit cooperation and compensation terms. contracts should have compliance protection clauses to safeguard corporate rights and interests in the event of regulatory inspections or disputes.
conclusion: balancing cost, security and compliance
when companies use malaysian servers to carry out charging and accounting docking , they need to strike a balance between cost, efficiency and compliance. through compliance processes, technical controls and strict reconciliation audits, operational risks can be minimized while ensuring business scalability and audit traceability, laying the foundation for long-term stable development of the enterprise.
- Latest articles
- Detailed Operation Guide On How To Use Basic Settings And Remote Connection In Korean Vps
- Comprehensive Solution For Network Link Selection And Transmission Optimization From Vietnam Cloud Server To Mainland China
- Us Cn2 Server Deployment Guide Practical Steps From Purchase To Online
- Optimization Strategy For Combining Vps Server Access To The United States And Local Cdn In Overseas Site Deployment
- Performance Cases For Media And Streaming Platforms Using Vietnamese Cn2 Servers
- How To Change The Name Of The Taiwan Server In The Control Panel With Detailed Step-by-step Instructions
- Actual Test Shows How Much Faster Hong Kong’s Cn2 Line Can Be Delay Evaluation
- Description Of Legal Compliance And Responsibility Boundaries Involved In Us High-defense Server Q&a Questions
- How To Deploy A High-availability Architecture On Tk Malaysia Vps To Reduce The Risk Of Downtime
- From A Technical Perspective, We Will Explain Which Vps In Hong Kong Is Reliable And Compare Bandwidth And Protection.
- Popular tags
-
Analysis Of Three Network Cn2 Malaysia’s Access Advantages And Enterprise Implementation Plan
detailed analysis of the network advantages, latency and bandwidth performance of <b>the three networks cn2</b> in <b>malaysia</b> , and provides enterprise-oriented deployment and <b>server</b> selection, cost and operation and maintenance solutions to help enterprises achieve the best cost performance. -
Comparing Domestic And Foreign Suppliers Malaysia Cn2 Vps Price And After-sales Service Difference Analysis
focusing on cn2 vps in malaysia, we compare the differences between domestic and foreign suppliers from five issues including price, network quality, billing method, after-sales response and selection strategy, and provide actionable measurement indicators and suggestions. -
Details You Need To Pay Attention To When Choosing An Anti-blocking Server In Malaysia
the details and answers to questions you need to pay attention to when choosing a malaysian anti-blocking server to help users better choose the right server.